
Life Insurance Terminal Illness Coverage Explained
A Terminal Illness Benefit generally applies when the insured is diagnosed with a medical condition that is expected to result in death within a specified
Keep Learning, Keep Growing

A Terminal Illness Benefit generally applies when the insured is diagnosed with a medical condition that is expected to result in death within a specified

Stay updated with the most important Daily Current Affairs of 18 May 2026 for all competitive exams including UPSC, SSC, Banking, Railways, Defence, State PCS,
A Terminal Illness Benefit allows a policyholder to access a portion of their life insurance death benefit while still alive if diagnosed with a terminal

Stay updated with the most important Daily Current Affairs of 17 May 2026 for all competitive exams including UPSC, SSC, Banking, Railways, Defence, State PCS,

Economic Insights: Navigating the World of Finance
Are you intrigued by how money moves and shapes the world around us? Dive into the realm of
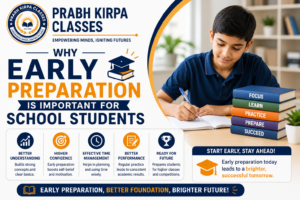
Education is the foundation of growth, knowledge, and success. Every student dreams of achieving good marks, building a successful career, and gaining confidence in life.

Education is one of the most powerful tools for building a successful future. It helps individuals gain knowledge, improve skills, and create better career opportunities.
Education has always been one of the most important foundations for personal growth and career success. Over the years, the methods of teaching and learning

An Accelerated Death Benefit (ADB) Rider allows a policyholder to access a portion of the life insurance death benefit while still alive if certain qualifying
Living benefit riders allow policyholders to access a portion of their life insurance benefits while they are still alive under specific medical conditions.
The three
Dual Purpose Life Insurance provides protection in two ways:
✔ Death Benefit – Financial support for beneficiaries after the insured’s death
✔ Living Benefits
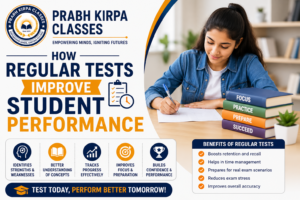
Academic success is not only about studying chapters and completing homework. One of the most important parts of learning is evaluating how much students actually
In today’s competitive academic environment, students face increasing pressure to perform well in school exams, board examinations, and competitive tests. Many students believe they can
Pause & Reflect: Delayed Intimation highlights an important reason for insurance claim complications and repudiation—informing the insurer too late about hospitalization, accident, or medical treatment.
Technology has become an essential part of modern life. From education and business to communication and entertainment, computers are used everywhere. In today’s digital world,

Success in academics is not only about studying for long hours. The real difference comes from studying smart, staying consistent, and following the right learning

Pause & Reflect: Document Discrepancies focuses on a common but often overlooked reason for insurance claim delays and repudiation—inconsistencies between submitted documents.
Even minor mismatches
Education is one of the strongest foundations for building a successful future. Every student has the potential to achieve great results, but proper guidance, motivation,

Education plays one of the most important roles in shaping a student’s future. In today’s competitive academic environment, students not only need hard work but
Pause & Reflect: Missing Documents highlights one of the most common and preventable reasons for insurance claim delays and repudiation—incomplete or missing paperwork.
Even a